The State Police Want to Crack Your Phone
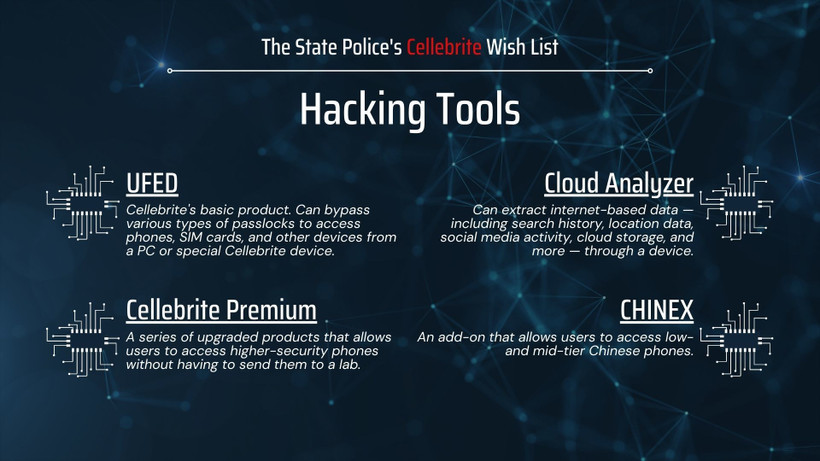
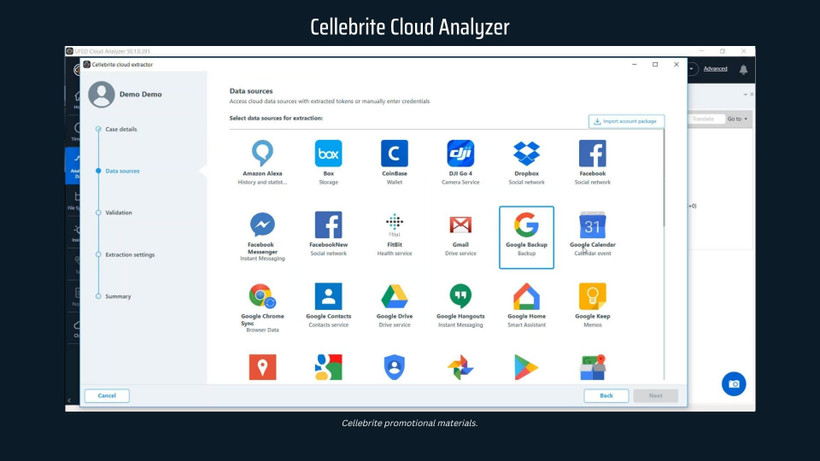
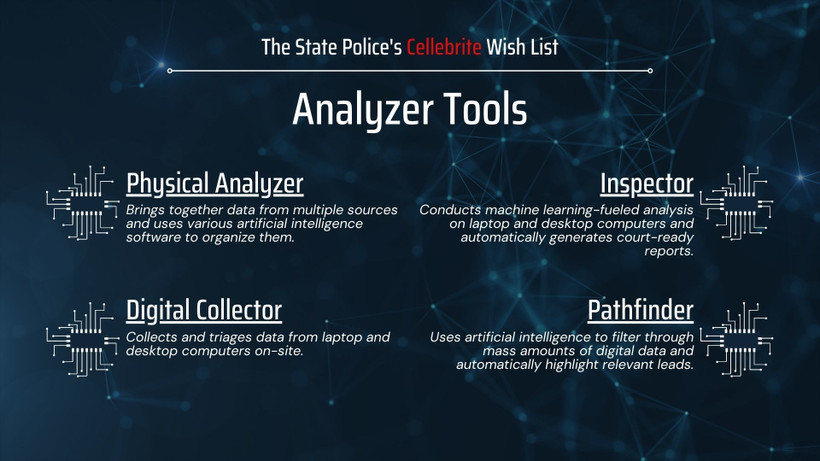
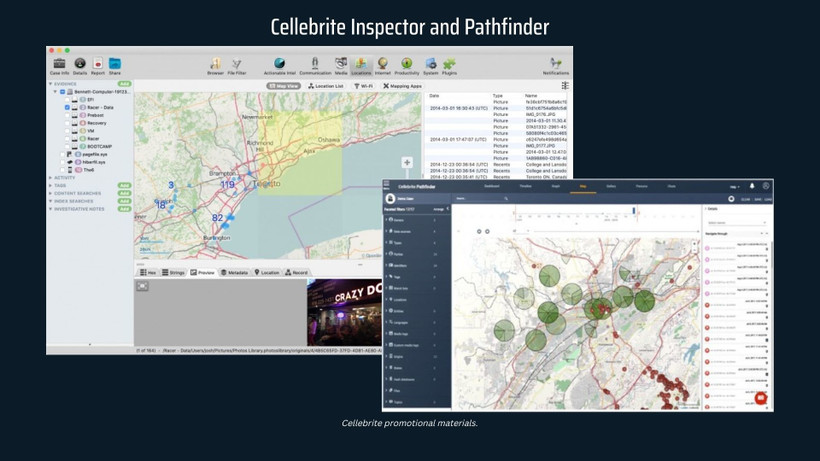
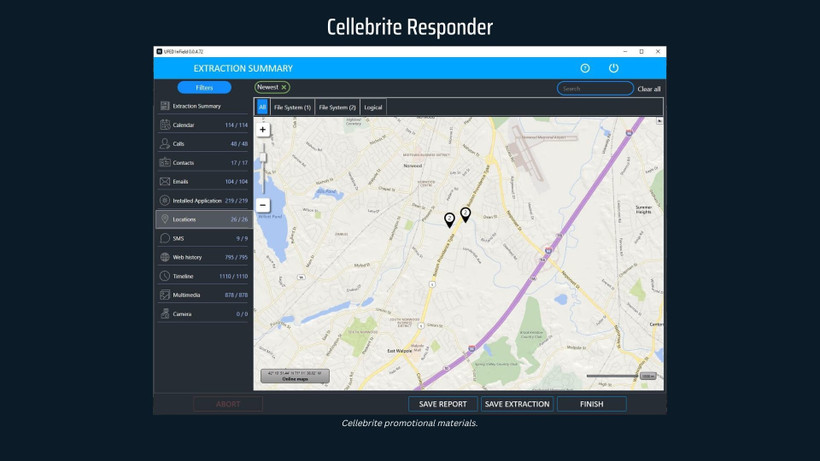
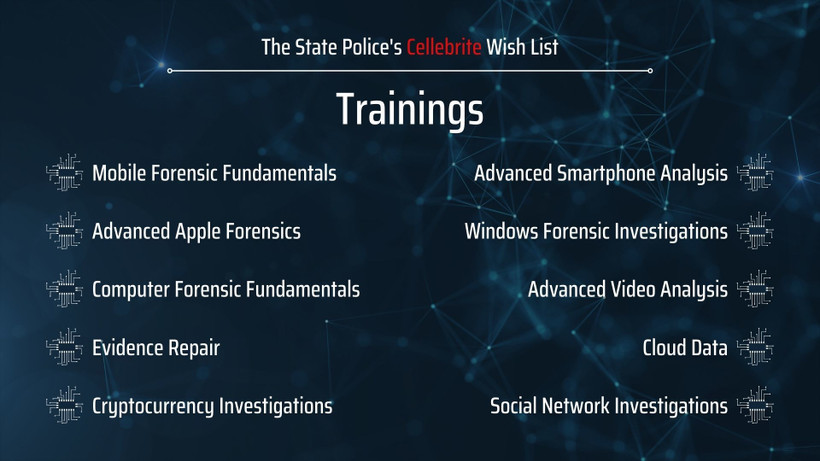
The Israeli firm Cellebrite offers tools that unlock data, trawl search histories, and perform facial recognition. The New York State Police are in the market.

- As State Police Expand Surveillance, Privacy Advocates Turn to US Congress
- Hochul Wants More Police Surveillance. Legislators Want Boundaries.
- The State Police Are Watching Your Social Media
- The State Police Sent You a Friend Request
- Kathy Hochul Is Ready to Spend Millions on New Police Surveillance
Technology moves so much faster than anything in the law or politics.
New York’s search warrant statute was written more than 50 years ago, before the proliferation of modern computers.

Previously unreleased disciplinary files expose officers who beat, slap, and pepper spray the residents they’re supposed to protect. Most are back at work within a month.
Local regulations haven’t kept up with the rollout of new surveillance tech. Some reformers see Washington as their best hope.
Stark disparities in access to life-saving medication for opioid addiction persist between facilities — and racial groups.
A version of good cause eviction and new hate crimes are in; new taxes on the wealthy and education cuts are out. Here’s where things landed in this year’s budget.
The Assembly rejected legislation that would have sped up New York’s transition away from gas.
Low-wage manual laborers can sue to make their bosses pay them weekly. Hochul’s late-breaking budget addition may undermine that right.